The Best Time to Hire a CISO Was Yesterday. The Second-Best Time Is Now.

When a cyberattack takes hold, it’s enough to ruin a company’s reputation for a long while. This causes trust in the company to plummet in turn. Thankfully, hiring a chief information security officer could put your company one step ahead in the endless quest for cybersecurity.
The only constant in life is change, said the Greek philosopher Heraclitus — an aphorism that’s especially true when it comes to cybersecurity. The fear of change is also constant, he said. Consider that most Fortune 500 companies lack a genuine long-term commitment to cybersecurity. In the meantime, data breaches cost companies nearly $350 million and result in stock price drops of 7.5%, according to Bitglass.
In addition, just one successful cyberattack can monumentally damage a company’s reputation, causing customer trust to plummet. After all, who wants to entrust sensitive information to a company with known cybersecurity weak spots?
The cyberattacks of the future will only become more sophisticated, and bolstering your cybersecurity efforts to combat those attacks starts with getting the right people in the right seats. At my company, I head up executive search assignments for IT and cybersecurity leadership roles. Here’s what is perhaps my biggest recommendation: Hire a chief information security officer, or CISO. This person will work to ask — and answer — key questions for your organization, such as:
- Who’s trying to hack your data, anyway?
- What might their strategy be?
- Have they tried to hack your company already? If so, in what ways?
- What kinds of information are they interested in stealing?
- What might their motive be?
- When is your business especially vulnerable?
- Will you be hacked because someone is especially skilled at what they do, or because you didn’t take proper precautions?
Untapped Opportunities Abound
CISOs help their organizations anticipate and reduce risk tied to the above questions and beyond, and particularly for risks of the digital variety. A good CISO has both senior-level and teamwide conversations about risk. However, for your CISO to be better than good, you have to integrate them into the executive team — something surprisingly few companies do.
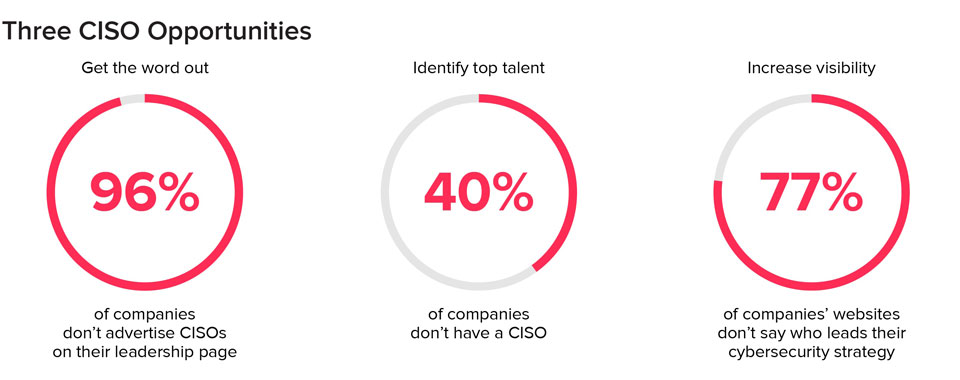
The good news? More than 60% of companies have added a CISO to their team, according to the Bitglass study mentioned above. But only 4% advertised the role on their leadership page. In fact, 77% had zero information on their website about who was in charge of their cybersecurity strategy. That’s a major missed opportunity, and it’s time to flip the switch.
When your CISO owns the risk, monitors the risk, and is empowered to take necessary action, you’ll realize the full benefits of the role. For example, I once talked with a CISO at a large U.S. retailer that was going through an acquisition. He inserted himself in the process to evaluate elements of risk that the executive team had glossed over. When he did his due diligence, he realized the company they were about to acquire had multiple third-party supply chain risks. Although he pushed the acquisition back several months, he also saved his employer from a massive headache.
Another CISO at a large software company in the U.K. realized there was no integration between the security and software development functions. He inserted his cyber team into parts of the software function to ensure the product wasn’t released to market before it had been signed off by the security function, thereby reducing the risk in the products the company was releasing.
Determine What Kind of CISO You Need
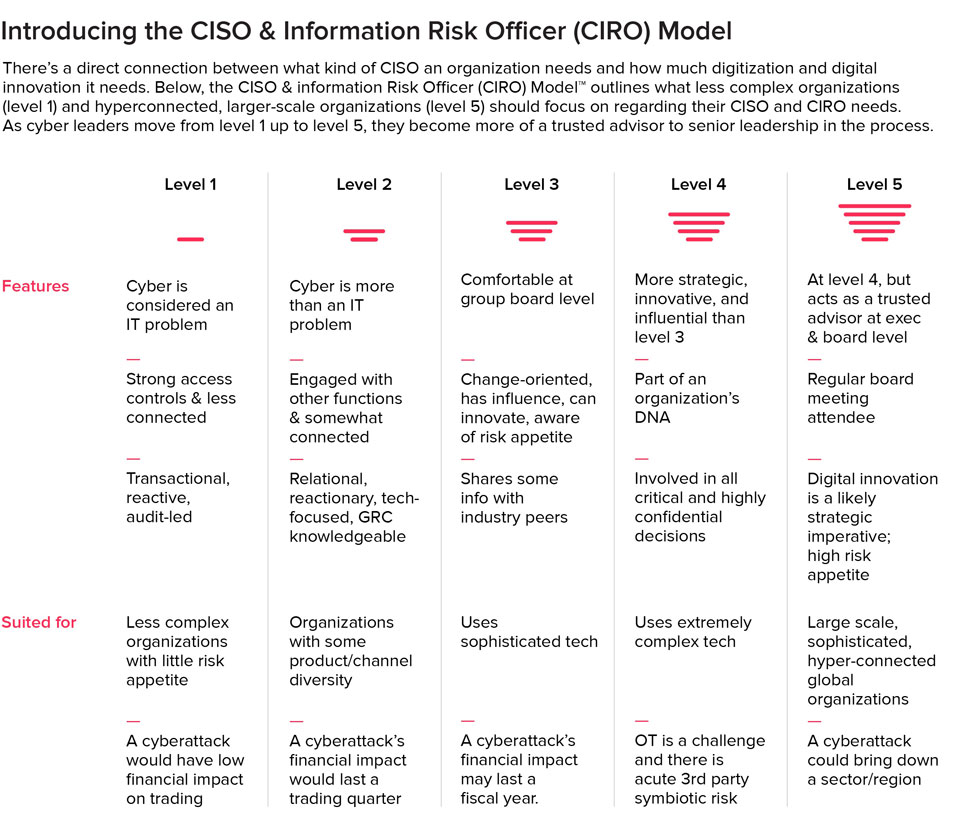
Different organizations require different abilities in their CISOs. So how can you determine what kind of CISO you need to effectively protect your company from risk? In an attempt to answer this question myself, I created a five-level CISO maturity model using psychometric data, artificial intelligence, and facial expression detection to draw a psychological profile that is then compared to the profile of a typical CISO. Using this framework, IT leaders can determine where their organizations stand on the model and what they need to do to move to the next stage on the spectrum.
It’s important to keep in mind that not every organization will require a level-five CISO. Perhaps you’re a smaller business that just needs a level-one CISO to monitor the cyber aspects of IT and infrastructure. That’s perfectly valid.
Other organizations (such as large financial institutions) have more complex cyber needs, and they’ll likely require a level-five CISO. That’s because cyberattacks targeted at highly connected international organizations can profoundly impact supply chains, adjacent industries, and even society at large. These companies need a premier CISO who understands the technical aspects of attacks, communicates that risk effectively in a way nontechnical employees will understand, and takes action at all company levels.
Determining your own needs means grasping your exposure risk. How much riskier is your business or industry going to get in the next five to 10 years? If you are not growing or getting more complex, then you probably don’t need a higher-level CISO.
It’s also a good idea to consider succession planning when determining the right type of CISO. Competent CISOs are likely to be constantly recruited. If your current CISO leaves, who will take over, and what does that look like? Hiring a great CISO is more complicated than placing a few LinkedIn ads. People inevitably move on from their current employers, so enact a three-year development program to prepare for change now.
“All is flux, nothing stays still,” said Heraclitus. Indeed, change in cyberspace is constant, and a CISO’s strategies must be, too. The CISO of yesterday was considered to be a data firewall. Now, CISOs are the cybersecurity thought leaders the future urgently demands.
Written by Tim Cook.
Add CEOWORLD magazine to your Google News feed.
Follow CEOWORLD magazine headlines on: Google News, LinkedIn, Twitter, and Facebook.
This report/news/ranking/statistics has been prepared only for general guidance on matters of interest and does not constitute professional advice. You should not act upon the information contained in this publication without obtaining specific professional advice. No representation or warranty (express or implied) is given as to the accuracy or completeness of the information contained in this publication, and, to the extent permitted by law, CEOWORLD magazine does not accept or assume any liability, responsibility or duty of care for any consequences of you or anyone else acting, or refraining to act, in reliance on the information contained in this publication or for any decision based on it.
Copyright 2024 The CEOWORLD magazine. All rights reserved. This material (and any extract from it) must not be copied, redistributed or placed on any website, without CEOWORLD magazine' prior written consent. For media queries, please contact: info@ceoworld.biz
SUBSCRIBE NEWSLETTER